There has been a significant rise in adversary-in-the-middle (AiTM) phishing attacks. Specifically, Salesforce and SugarCRM users should be on heightened alert. In this type of attack, a cybercriminal uses embedded links to lead an end user to a phishing site to steal their credentials.
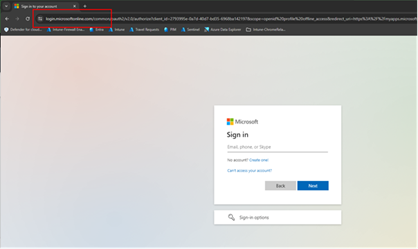
Microsoft URL for Authentication: Please pay close attention to the correct Microsoft URL for authentication. It is:
login.microsoftonline.com/…………..
Warnings about AiTM Threats
In recent years, Microsoft has issued warnings about threat actor groups that have been involved in these adversary-in-the-middle attacks. Storm-1575 is a cybercriminal group responsible for developing, supporting, and selling a phishing-as-a-service platform called Dadec. This platform has adversary-in-the-middle (AiTM) capabilities and has been active since May 5, 2023.
Another group associated with harvesting and credential phishing activity is Storm-0485. It’s particularly alarming that members of this group have been able to get around some of the multi-factor authentication (MFA) protections of users who fail to verify falsified links.
Microsof’s warning also outlines that end users have been lured through voice messages, Microsoft Teams communications, and shared documents. Members of Storm-0485 have also provided links in phishing emails that abuse Google for redirection and include domain generation algorithms (DGA), which create random domains to use for phishing attacks.
Protect Yourself and Your Data
- Always verify. You must NEVER click on any links found in any unexpected emails, even if the message appears to come from someone you trust. When in doubt, always verify. A simple verification email or phone call could prevent a data breach.
- Be suspicious of any email marked as [EXTERNAL] in the subject line. Even companies that rely on strong verification tools, such as Proofpoint or Mimecast, are at risk. These tools rely on signatures, rules, and blacklists. A URL may take time to be determined as malicious, resulting in you becoming the victim of the attack.
- If you are uncertain about an email, contact your company’s IT or cybersecurity team for further assistance.